The sensible house makes many issues extra handy inside your individual 4 partitions, but in addition creates quite a lot of extra technical issues — not least with regard to the safety of your individual information.
The marketplace for sensible house options is split into two giant teams:
- One contains management methods which can be completely put in by licensed tradespeople.
- The opposite group contains parts from numerous producers that may be simply retrofitted by non-professionals and rework easy lights or thermostats into sensible gadgets.
With the latter gadgets, there are an entire vary of annoyances that the majority customers don’t take into consideration when shopping for. This brief information reveals firstly how one can reduce the dangers before you purchase, and secondly how you will discover and shut weak factors in current gadgets.
Additional studying: The way to maintain your property community safe: Sensible methods and settings
Compelled to make use of the cloud? Finest to modify off
Many producers pressure prospects to permit their gadgets to hook up with the web as a result of that is the one option to management them from any location. For instance, the gadgets from Chinese language producer Xiaomi (Mi Lamp and followers) can solely be managed through a smartphone app (except you utilize the switches on the gadgets, however you don’t want a sensible house for that).
Sadly, establishing the app and due to this fact utilizing voice assistants corresponding to Alex or Google House is obligatory.
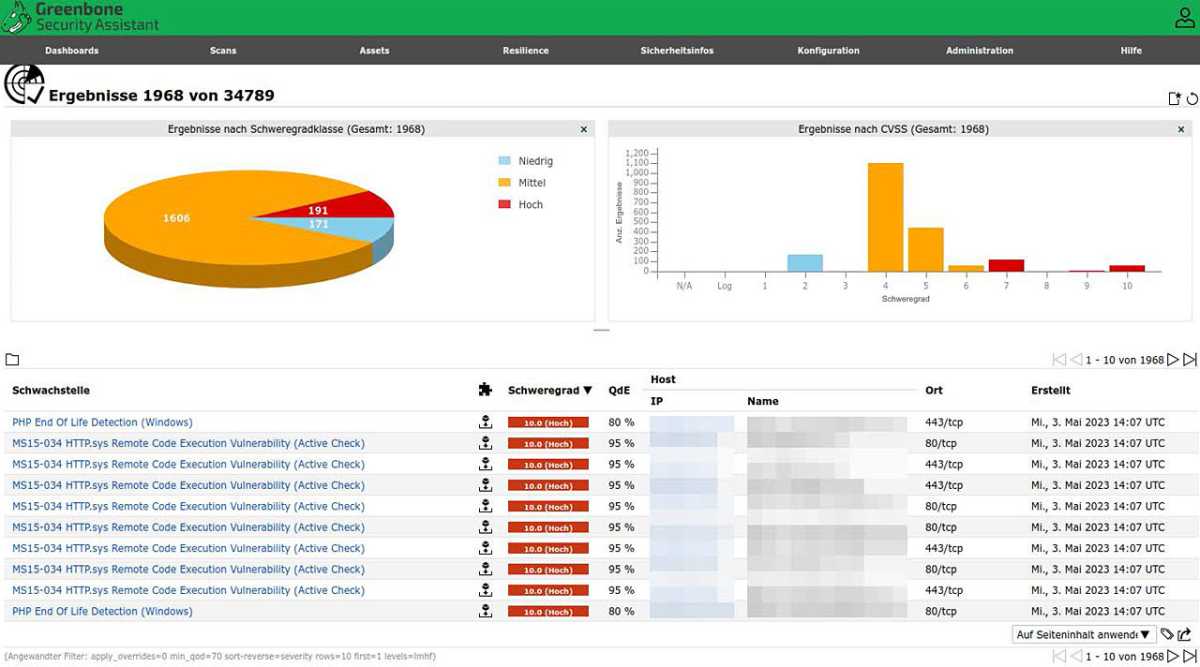
Open VAS (additionally included with Kali Linux) analyzes the native community and all gadgets for vulnerabilities and configuration errors.
Open VAS (additionally included with Kali Linux) analyzes the native community and all gadgets for vulnerabilities and configuration errors.
IDG
Open VAS (additionally included with Kali Linux) analyzes the native community and all gadgets for vulnerabilities and configuration errors.
IDG
IDG
It’s due to this fact hardly stunning that the Shodan search engine may also be used to simply acquire insights into different folks’s rooms — due to unsecured and barely up to date webcams.
It’s advisable to learn the critiques earlier than making a purchase order and to concentrate to such a compulsion to make use of the cloud. There must be no want for this inside your individual 4 partitions.
With different bridges such because the Raspbee or Conbee, management can be attainable with out the cloud (supplied the gadget is appropriate).
And you need to all the time ask your self whether or not a perform is definitely wanted: When you’re searching for handy temperature management for heating or air flow, you don’t essentially want a perform that acknowledges through smartphone that you’re approaching the constructing (which may solely be achieved by connecting through the web).
After we speak about safety dangers right here, we’re not simply speaking concerning the safety of the information inside your individual community. If hijacked gadgets within the community belong to a botnet, they’ll now not be used, to not point out all of the authorized issues.
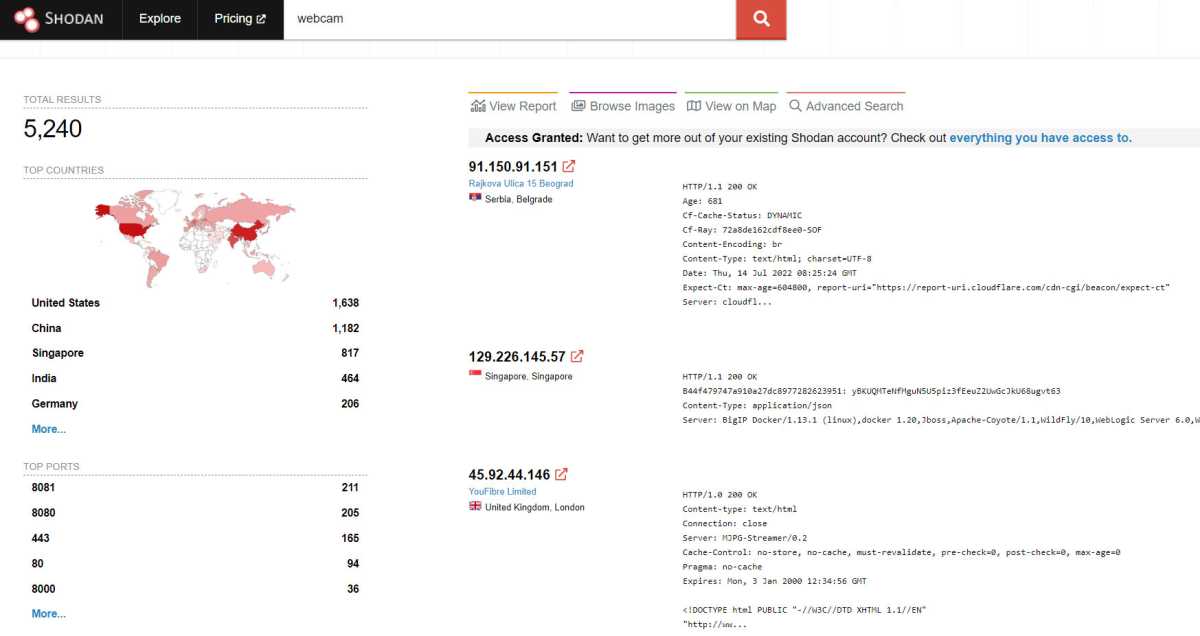
The Shodan search engine produces astonishing outcomes. Inadequately secured webcams usually permit folks to look into different folks’s houses.
The Shodan search engine produces astonishing outcomes. Inadequately secured webcams usually permit folks to look into different folks’s houses.
IDG
The Shodan search engine produces astonishing outcomes. Inadequately secured webcams usually permit folks to look into different folks’s houses.
IDG
IDG
Wi-Fi? A query of connection
Safety dangers might be minimized by selecting the best {hardware} and its connectivity. At first look, gadgets that hook up with Wi-Fi appear handy. Though an app is normally required to set this up, it’s only used to retailer the community key within the gadget.
Nevertheless, utilizing Wi-Fi additionally exposes the gadgets to all of the assaults that attackers use towards a wi-fi community.
Within the descriptions of their gadgets, producers solely emphasize the comfort and ease of setup. References to the usual used have a tendency to stay hidden. Units that comply with a unique customary, corresponding to Zigbee, are higher than having numerous gadgets in the home that hook up with the house’s personal Wi-Fi.
Tip: If it completely must be Wi-Fi (as a result of you could have already bought the lamps or radiator controls), you’ll be able to isolate the parts in a separate community. The Fritzbox, for instance, has an extra “visitor community” that can be utilized for these gadgets.
The router as a weak level
In all efforts to attain better safety for IoT gadgets inside your individual 4 partitions, you need to all the time prioritize the router. That is the place the largest vulnerabilities are normally hidden.
These embrace forgotten port authorizations that you just created as soon as to strive one thing out. Along with the port shares, additionally take note of protocols which can be notably steadily exploited by attackers. These embrace UPnP (Common Plug and Play), for instance.
UPnP makes it simpler for gadgets inside a community to seek out one another and set up connections. Nevertheless, if a tool (and its firmware) is allowed to arrange port sharing independently, it’s conceivable that this easy protocol may also be accessed externally. That is then straightforward prey for any bot.
One of the best technique for hardening the community is to persistently begin from a blacklist. Swap off all exterior connections to gadgets that aren’t completely needed for performance. In brief: All the pieces that’s not wanted must also be switched off.
Transparency via your individual platforms
Each producer recommends a separate app for controlling the gadgets. With numerous gadgets, that is something however sensible and handy in the long term. Apple’s Homekit or Google House and Alexa purpose to rectify this, at the price of now not having the ability to maintain potential vulnerabilities.
Safety-conscious customers with experience can use purposes corresponding to Open HAB, Domoticz, or iobroker to place collectively a custom-made surroundings that’s simpler to keep up, affords extra transparency, and in addition allows cross-device processes.
Detect and shut vulnerabilities
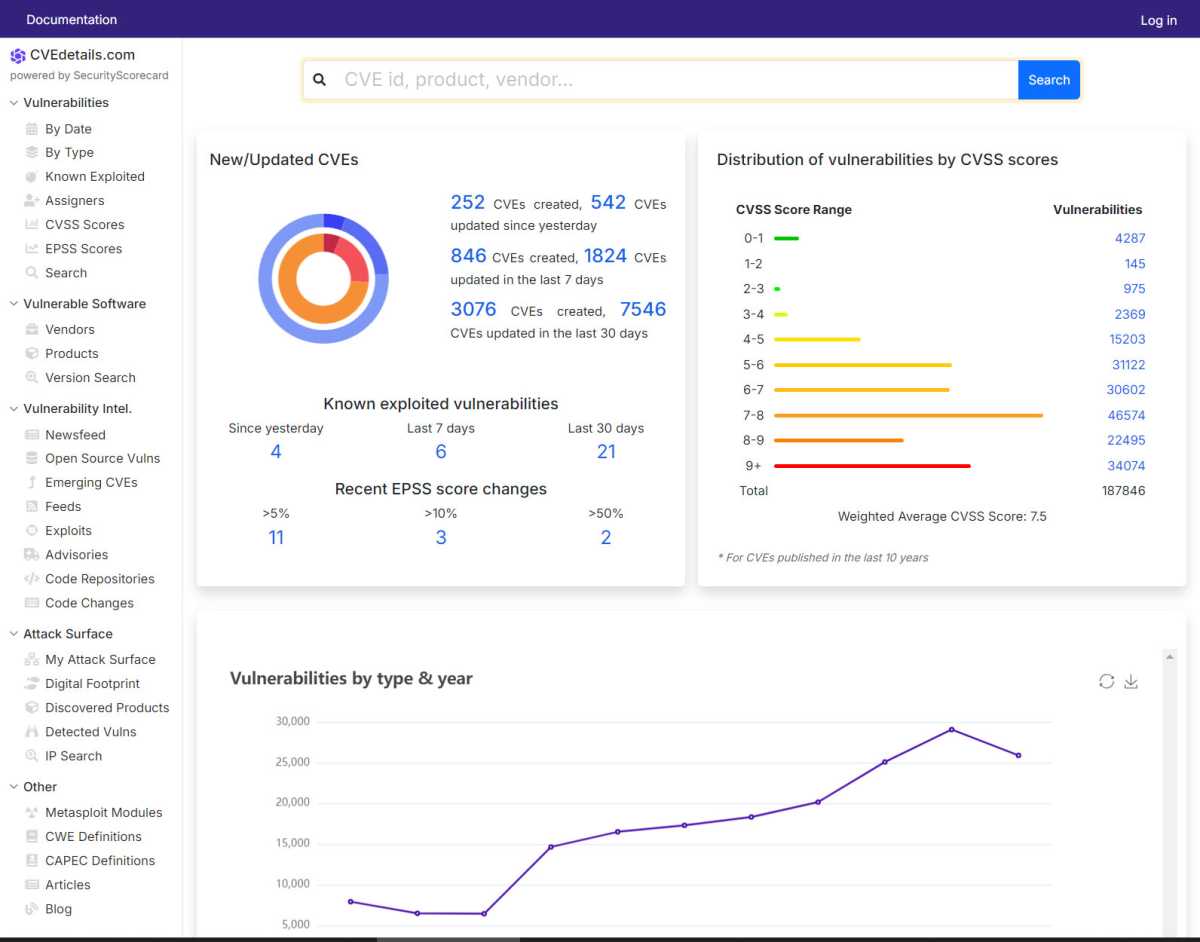
Instruments corresponding to Open VAS normally present distinctive CVE numbers for vulnerabilities discovered, which you’ll be able to then use to seek for patches and attainable options.
Instruments corresponding to Open VAS normally present distinctive CVE numbers for vulnerabilities discovered, which you’ll be able to then use to seek for patches and attainable options.
IDG
Instruments corresponding to Open VAS normally present distinctive CVE numbers for vulnerabilities discovered, which you’ll be able to then use to seek for patches and attainable options.
IDG
IDG
If you wish to discover out about potential vulnerabilities within the gadgets and methods you utilize, you want safety options. Open VAS (“Open Vulnerability Evaluation System”), which is accessible beneath the business label of the corporate Greenbone, is one such vulnerability scanner.
You’ll be able to set up it in your system through Docker or from the supply code. Alternatively, you should use the well-known Kali Linux distribution, which additionally has the scanner on board.
Scanning takes some time, however on the finish you’ll obtain a complete and graphical report to acknowledge current vulnerabilities. Every vulnerability is characterised by a novel CVE quantity. You’ll be able to then discover out about attainable injury and also can seek for patches on the web.
However, it’s harder to detect attainable ongoing assault makes an attempt or anomalies within the community. On the one hand, you want a device that scans the information packets and factors out attainable issues.
Secondly, information of protocols and community visitors is required with a view to interpret the outcomes appropriately. Beneath Kali Linux, for instance, you’ll be able to set up the Suricata program, which enjoys a wonderful popularity. Nevertheless, the precise work solely begins after set up, which is past the scope of this text.
This text initially appeared on our sister publication PC-WELT and was translated and localized from German.













